Tag: Security
STOP BACK OFFICE THEFT

5 Tips to Help Stop Theft in Your Back Office
It’s unfortunate, but even in today’s era of two-factor authentication and hyper-alert security, we still hear stories of physicians being defrauded by their employees. To help protect yourself from financial fraud, consider adopting these five approaches in your practice.
1) Cross-Train Your Employees
The most common place for fraud to occur is in the back office of small businesses where only one person handles the cash and books. Train more than one person on the cash conversion cycle. Rotate people through the various processes, too, so that no single person operates in a silo. When multiple people know the process, they can check each other’s work for mistakes and anomalies. Cross-training employees helps to create an open and transparent environment. It also reduces the chance of theft by assuring no one person wields too much power. Ultimately, it would be best if you also knew the process, so you can be an effective leader and fiscally responsible business owner
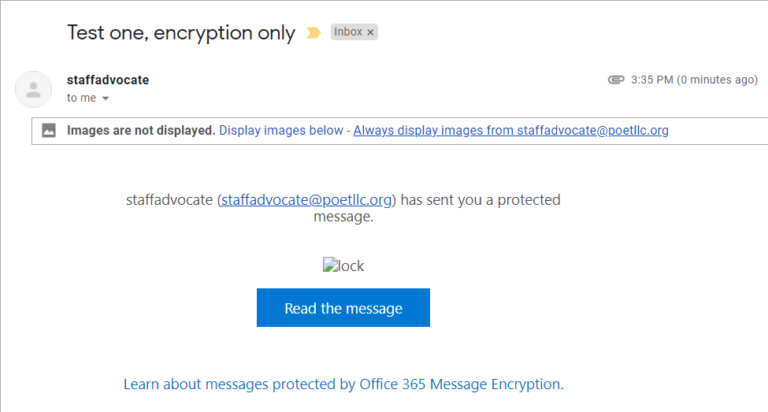
POET has a new way of encryption

Sometimes stuff happens that you really didn’t plan on.
Encrypted emails from POET will look a little different.
If you have any problems opening an encrypted email from us please let us know.
Below is a screenshot of what it will look like.
2022 Tech Trends from Iconic IT
The pandemic has sped everything up.
Here’s some of the big trends Iconic believes you’ll be seeing a lot more of in 2022:
1. Companies will invest more in cybersecurity insurance than ever before.
2. Cloud-based desktop software like Microsoft’s Cloud PC will grow in popularity.
3. Companies of all sizes will rely on SIEM cybersecurity defenses.
4. Mobile devices will become a bigger target for hackers.
With more employees than ever working remotely, they’re more likely to use poorly protected cell phones and computers on unsecured wifi. According to Digital Information World, 40 percent of mobile phones are prone to attack, and in need of better authentications and cybersecurity software.
5. AI-enabled cybersecurity software will help companies mitigate network threats in their networks, and the Internet of Things.
Emailing Archiving and Hippa Compliance
Make Sure email is a part of your cybersecurity stategy.

Email archiving is an automated process for preserving and protecting all inbound and outbound email messages (as well as attachments and metadata) so they can be accessed later. In other words, email archiving is storing emails and making them searchable.
Email archiving providers take this burden off organizations by storing emails on their servers while making them accessible to designated administrators in the organization. This is different than simply creating an email data backup. Data backups do not allow searching, so if a particular email needs to be found, it might take weeks for you to find it
Is email archiving required for HIPAA compliance?
DHS warns of Emotet

DHS warns that Emotet malware is one of the
most prevalent threats today (click to read the full article)
POET wanted to pass this on to you. It is an excellent article to use for ongoing security training.
DHS Warns the Emotet Malware is on of the Most Prevalent Threats Today 10/6/2020
[embeddoc url=”https://community.poetllc.org/wp-content/uploads/2020/10/Emotet-Malware-10062020.pdf” download=”all” viewer=”google”]
Beware Phishing Attempts in 2020
Rachel V. Rose, JD, MBA
January 13, 2020
Health IT, Pearls, Practice Management
According to the National Institute for Standards and Technology (“NIST”), phishing is defined as “[a] technique for attempting to acquire sensitive data, such as bank account numbers, through a fraudulent solicitation in email or on a web site, in which the perpetrator masquerades as a legitimate business or reputable person.” Often times, phishing attacks, especially those executed through email and unsecure websites, lead to the deployment of ransomware.
To view the entire article check out “Security” under the “Compliance” File.
OR
Beware Phishing Attempts 2020 01132020
[embeddoc url=”https://community.poetllc.org/wp-content/uploads/2020/02/new-phishing-article-01132020.pdf” download=”all” viewer=”google”]
Texas Lowers Reporting Threshold for Security Breaches, Texas Medicine January 2020
[embeddoc url=”https://community.poetllc.org/wp-content/uploads/2020/01/Texas-Lowers-Reporting-Threshold-for-Security-Breaches-By-Sean-Price-Texas-Medicine-January-2020.pdf” download=”all” viewer=”google”]
Recent Comments